SCIM is Done – Intro Q&A
SCIM is Done Intro & Q&A
Tuesday 1E
Convener: Kelly Grizzle
Notes-taker(s): Susan Carevic
Tags for the session - technology discussed/ideas considered:
Discussion notes, key understandings, outstanding questions, observations, and, if appropriate to this discussion: action items, next steps:
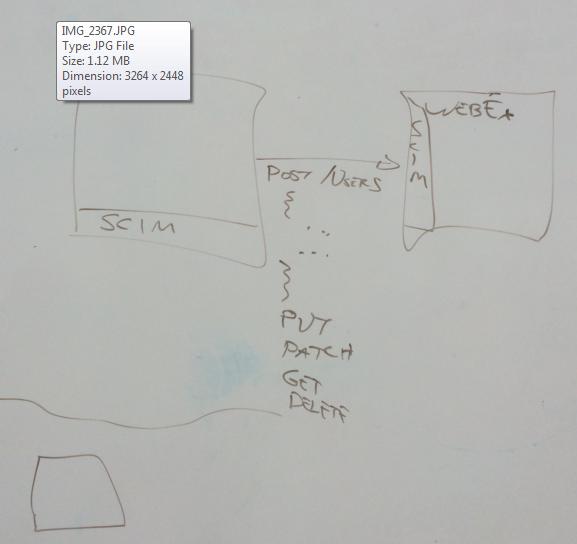
SCIM: System Cross Domain Identity Management
Basics: Take REST and combine with Identity. 2 major portions:
- Protocol: create/search/read/update
- Define Schemas: data types/define objects within server (Resource types). Extensibility
- Out of box: User and Group resource types
Origins: 5 years ago, desire to create standard for identity management\SCIM is complete as of September 2015!! Given 3 RSCs:
- Use case document 7642
- 7643: Schemas: data types, how to define types, what a user and group is (Standards Track)
- 7644: protocol document – how to use REST protocol (Standards Track)
Essence: cross-domain concept is what makes it interesting, as opposed to LDAP. HTTP/HTTPS: historically way to get to web//LDAP on cloud – a lot of non-standard things need to be done for this to work.
SCIM: design princiles: needed a schema model that had the core attributes everyone uses. Each domain is going to have completely different requirements. If I provision to your companies website, no need to rewrite my client. I can shove data to you, and you take what you need. Eliminates rigidity of XML format.
SCIM rules: generally favor service provider: Let server decide what it wants to do in favor of making the client’s life easier
Use cases:
Provisioning to multiple systems at same time/deprovisioning
Identity:What is a Cross domain identity: Federated Identity: lots of systems don’t work with federated identities, they need their own. Its having that same identity spread out across multiple systems. Each application tracks its users through its own set of identities. Each app will have certain set of information that app needs to function.. nothing to do with security functions it accepts.
SCIM: provides a common interaction mechanism for access to and management of heterogeneous identity environments.
Experience: We provision everyone into Google, BOX, O365, Amazon. Google and O365 don’t have SCIM interfaces. This is a matter of time. For many people, they can’t build until someone is provisioned. Incentive to have provisioning end point. Acceptance of protocols: need incentive
SCIM: What can you do (high level)
Client initiated. Client = Consumer of a service provider like (IDP). Piece of software running on behalf of the thing that managers the identity for a user (Http clients/services).
Example:
Cloud Provider: such as Salesforce, Webex, PING, … (uses SCIM)