RWOT 6 Biometric Principles White Paper Review
RWOT 6 Biometric Principles
Tuesday 2C
Convener: Jack
Notes-taker(s): Asem Othman
Discussion notes, key understandings, outstanding questions, observations, and, if appropriate to this discussion: action items, next steps:
In this session, we discussed the six principles for self-sovereign biometrics.
Biometrics are already here, and they will be used on the internet, whether we like it or not. They are already are; a lot of the current practices are bad and the centralized hosts know it. We know that centralized repositories of sensitive information are highly vulnerable and present irresistible targets, but better solutions are not available to current practitioners; they’re not even being considered. Fortunately, there are other fields that are already solving these problems, such as self-sovereign identity. We need to adapt their best practices to make biometrics safe and secure.
Therefore, during rebooting the web of trust workshop last month, a group start working on these principles (https://github.com/WebOfTrustInfo/rebooting-the-web-of-trust-spring2018)
The presenter discussed and enumerated the principles that have been detailed in the GitHub (https://github.com/WebOfTrustInfo/rebooting-the-web-of-trust-spring2018/blob/master/draft-documents/Biometrics.md)
one of the interesting suggestions is mentioning the different factors of usability of biometric traits and systems in order to be adopted in large scale.
Another suggestion is adding the concept of trust sensors similar to the Adhaar idea of registered devices that their identifiers should be added to the packet that will be sent along to the biometric data to the Adhaar database for verification of the data.
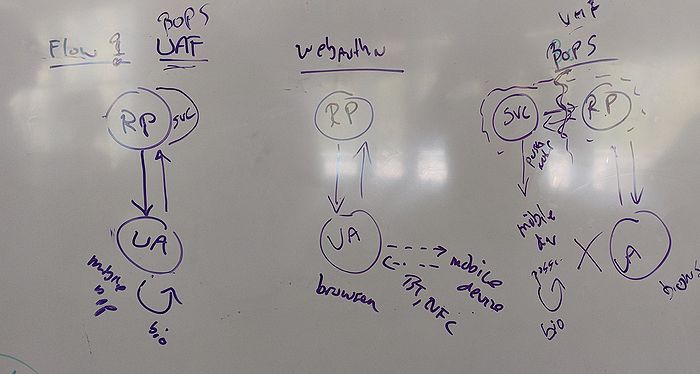
Finally, the presenter discussed few flows of using the biometric along with DID Auth. (check the picture)