DIDs For Everyday People
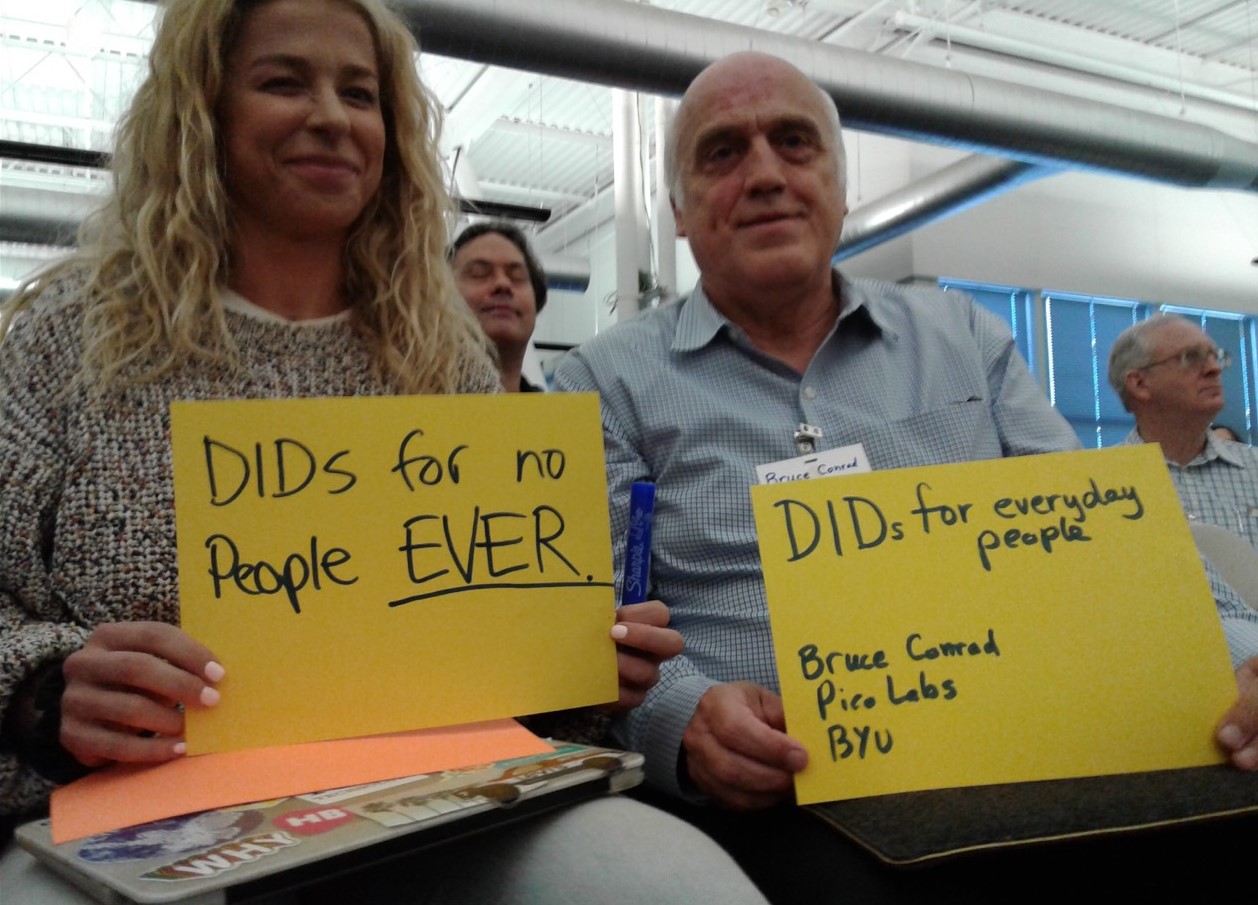
DIDs for Everyday People
Tuesday 5H
Convener(s): Bruce Conrad
Notes-taker(s): Bruce Conrad
Tags for the session - technology discussed/ideas considered:
Discussion notes, key understandings, outstanding questions, observations, and, if appropriate to this discussion: action items, next steps:
I presented 3 ways in which everyday people might be exposed to and/or use DIDs.
First, for a high school 50th reunion a year ago, I prepared one pico for each student pictured in the yearbook. When the name is selected on the home page, the yearbook picture is displayed. Each student for whom I could obtain an email address was sent a DID for their pico. They were invited to copy it and paste it into a certain place in order to identify themselves and then were asked to write a brief bio. About 15 of about 80 graduates did this. No one complained about the unusual look of their DID. A few protested that they were not technical and would not be able to do it. Most did not elect to participate.
Second, I used the page "did.html" which is included in every installation of the pico-engine, to show how a DID resolution scheme might work from within a browser. To see this page, install a pico engine using the command "npm install -g pico-engine" and then run it using the command "pico-engine" (in both cases without the quotes). Then visit this page by entering "localhost:8080/did.html" in a browser. The page describes how to configure your browser to use "web+did" as a protocol handler.
Third, using a Sovrin agent to handle the DID (and its public/private key pair) without showing it to the person. Using an agent running in the browser tab, we showed how Alice had a page of links to websites with which she had an established connection. A single click opens that website with Alice recognized (what we used to call "logged in"). We discussed how the connection would be established in a trusted environment in which Alice is invited, by a person she knows, to use a Sovrin agent app, on her phone, say, to make the connection.
More information can be found at http://picolabs.io and the code repository is at https://github.com/Picolab/pico-engine where you can find instructions for cloning and contributing. The simpler installation mentioned above is described at https://github.com/Picolab/pico-engine/tree/master/packages/pico-engine . Once you have picos, you can make them into agents following the instructions at https://github.com/Picolab/G2S . Running a pico agent within a browser tab can be done using software in the https://github.com/b1conrad/browser-agent repository.
Thanks to the participants for the many questions and explanations offered during the session. Phil Windley referred us to the Sovrin white paper at https://sovrin.org/library/lost-phone for what happens if Alice loses her agent. Thanks to Daniel Bluhm for explanations offered during the session.
For more information, please contact the author at bruce_conrad@byu.edu